The Beginner Malware Analysis Course
Related Terms : Overflow Malware Analysis
Overflow Tank Meaning Overflow Y Overlay Browser Support Overflow List First Kiss Zodiac Signs World Trigger 160 Overflow Space Meaning Reddit Genshin Impact Flutter Wrap Text In Container 1st Kiss Manga Romance Text Overflow Ellipsis Javascript Overflow Hot Tub Overflow Full Eng Sub Overflow Css Scroll Eco Forever Dragon Ball Z Java Overflow Handling Avatar Comics To Read Online Reddit Yugioh Read Comics Online Free In Hindi Overflow Overlay Alternative Andrew Rannells Mike Doyle Dc Comics Batman Read Online Free Overflow Css Hide Scrollbar Css Overflow Max Height Overflow Name Css Diy Overflow Filter Reddit Banned Countries Ley Line Overflow Genshin Reddit Overflow Ka Meaning Hindi Overflow Html Class Read Comics Online Free Manga Fairy Tail Characters Overflow Condition Meaning Kitchen Sink Universal Overflow Kit Javascript Overflow X Hidden Overflow Flag Clear Cvs Overflow Vaccine List Style Overflow X Javascript Genre Of Overflow Overflow Eps 7 Overflow Pipe On Hot Water Heater Dripping Overflow In Css Image Li Overflow Hidden Not Working Html Overflow Horizontal Scroll Strike The Blood Char Overflow Y Scroll Js Marvel Comics Infinity Gauntlet Read Online Overflow Period Meaning Overflow Css In React Dragon Ball Z Wooden Music Box Js Overflow Auto Scroll Star Wars Comic Books Online Free Anchor Link Overflow Hidden Avatar Comics Read Online Free Andrew Rannells King George Overflow In Linked List Buffer Overflow Info Javascript Print Overflow Reddit Ufc Strike The Blood All Characters Html Overflow Max Height Star Wars Marvel Comics Online Free Overflow X Visible Meaning Strike The Blood Raw Overflow Hidden Html Alternative To Manga Rock One Piece Chapter 973 Explained Stack Overflow Handling Java Overflow Hidden On Absolute Elements Overflow Pipe On Hot Water Heater Leaking Overflow Straw Game Overflow Download Video Overflow Meaning In English Star Wars Legends Comics Online Free Detect Overflow With Javascript Overflow Religious Meaning Css Div Horizontal Overflow Html Overflow Padding Reddit Xiaomi Overflow Hidden List Marvel Deadpool Comics Read Online Is Fairy Tail Manga Different From Anime Download Overflow Eps 4 Html Overflow Exception Jquery Mobile Overflow Scroll Css Overflow Resize Read Marvel Dc Comics Online Free Stack Overflow Javascript Calculator Adding Overflow To Aquarium Overflow Anime Episode 7 Sub Indo Overflow Css Que Es Overflow Not Hidden Strike The Blood Mal Overflow Meaning Of In Hindi Overflow In Java Number The Overflow Game Andrew Rannells Voice Acting Readcomiconline Star Wars Legacy Liveoverflow Html Overflow Hidden Horizontal Scroll Javascript Overflow X

Mar 16 2021 Attackers who can reach TCP port 3080 can send a specially crafted packet to trigger a buffer overflow corrupting the stack overwriting ECX register.
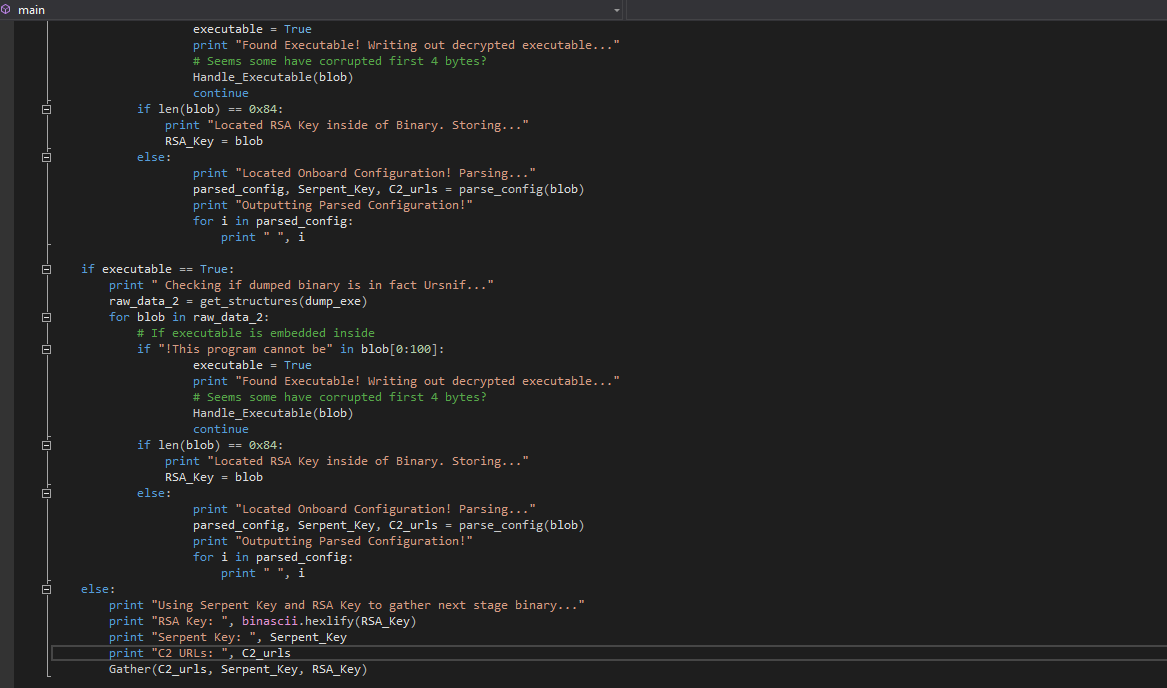
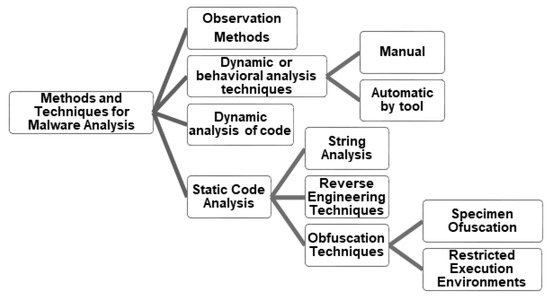
Javascript overflow x. Ive developed a console application that does a lot of routines but the Antivirus detected it as a malware of type GenVariantUrsu56053. This article provides an overview of various techniques that can be used to mitigate buffer overflow vulnerabilities. CTF solutions malware analysis home lab development.
About a month ago I used PyInstaller and Inno Setup to produce an installer for my Python 3 script. As the name hints at Laboratory is largely about exploiting a GitLab instance. CVE-2021-21983 - VREALIZE API FILE RCE EXPLOIT - HTTP REQUEST.
Algorithms for Exploit Packs and redirection malware detection. Laboratory hackthebox Laboratory ctf gitlab nmap vhost gobuster searchsploit cve-2020-10977 deserialization hackerone docker ruby irb suid path-hijack. Research and Analysis Research News and Perspectives Security Reports Security News Zero Day Initiative ZDI Blog Research by Topic.
It may be dropped by other malware. After successful exploiting a Microsoft Exchange Server vulnerability for initial accesses a malicious cyber actors can. Cyber securitys comprehensive news site is now an online community for security professionals outlining cyber threats and the technologies for defending against them.
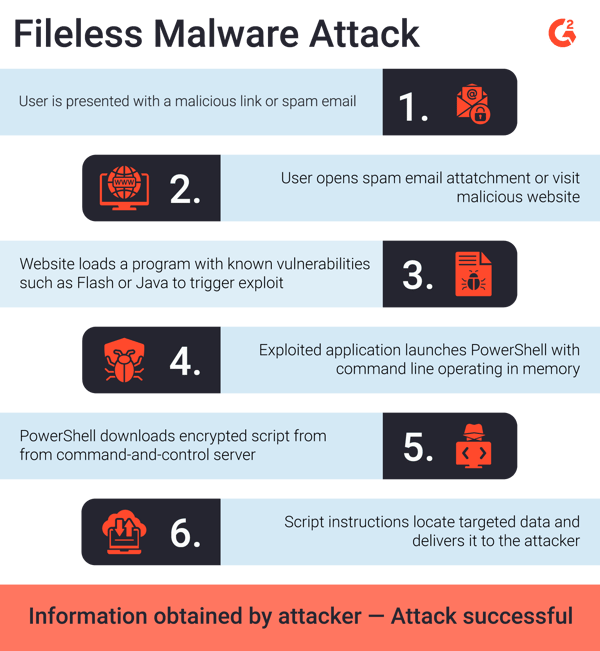
In other words you can create a malicious m3u file feed it into the utility and trigger the exploit. This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites. Are there any Vulnerabilities currently present on the server.
Detection for ActiveX attacks and Buffer Overflow. Mitigate Microsoft Exchange Server Vulnerabilities. The latest cybersecurity threats.